"The modified plugins lay dormant for eight months to evade quick detection while allowing thousands of WordPress users to install them before activating."
"Ginder found that the plugin had been operating legitimately until August 8, 2025, when malicious code was added to grant the attacker a backdoor."
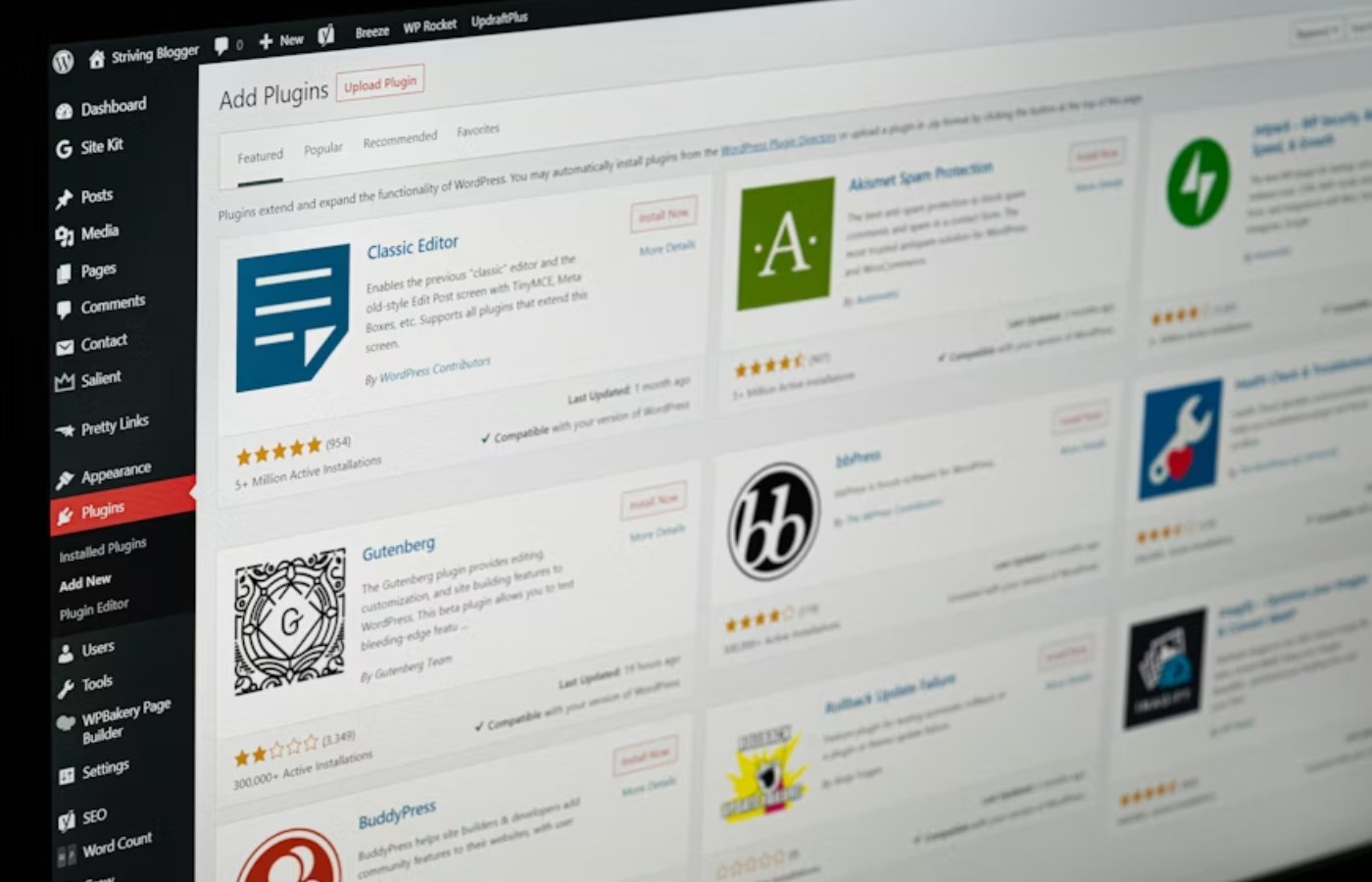
A web developer discovered numerous malicious WordPress plugins containing backdoors that compromised thousands of websites. These plugins, part of the Essential Plugin portfolio, were modified after a change in ownership. They remained dormant for eight months, allowing widespread installation before activation. The attackers controlled the plugins rather than directly hacking websites, exemplifying a supply-chain attack. WordPress has since closed the affected plugins. A specific plugin, Countdown Timer Ultimate, was flagged for unauthorized access, despite a forced update that failed to remove the malicious code.
Read at TechRepublic
Unable to calculate read time
Collection
[
|
...
]