#swift-package-manager
#swift-package-manager
[ follow ]
fromTheregister
1 month agonpmx alternative to npmjs released to fix pain of rpm
npmx is about speed and simplicity. It gives you useful data like install size, module format and outdated dependencies ... we're also building social features into npmx because open source is better when it's easier to connect with the people behind the packages.
Node JS
fromDevOps.com
1 month agoChainguard Expands Repository to Add More Secure Open Source Libraries - DevOps.com
Chainguard has rebuilt nearly one million unique versions of Java dependencies, including enterprise essentials such as Spring Boot, Jackson, Apache Commons, and Log4j, using the Chainguard Factory, an automated platform for creating software builds based on code originally found in open source software repositories.
Information security
fromTechzine Global
1 month agoGo developer questions effectiveness of Dependabot
Dependabot sounded the alarm on a large scale. Thousands of repositories automatically received pull requests and warnings, including a high vulnerability score and signals about possible compatibility issues. According to Valsorda, this shows that the tool mainly checks whether a dependency is present, without analyzing whether the vulnerable code is actually accessible within a project.
Information security
fromComputerworld
2 months agoJamf has a warning for macOS vibe coders
But like everything else in life, there will always be a more powerful AI waiting in the wings to take out both protagonists and open a new chapter in the fight. Acclaimed author and enthusiastic Mac user Douglas Adams once posited that Deep Thought, the computer, told us the answer to the ultimate question of life, the universe, and everything was 42, which only made sense once the question was redefined. But in today's era, we cannot be certain the computer did not hallucinate.
Artificial intelligence
fromThe Hacker News
1 month agonpm's Update to Harden Their Supply Chain, and Points to Consider
Let's start with the original problem Historically, npm relied on classic tokens: long-lived, broadly scoped credentials that could persist indefinitely. If stolen, attackers could directly publish malicious versions to the author's packages (no publicly verifiable source code needed). This made npm a prime vector for supply-chain attacks. Over time, numerous real-world incidents demonstrated this point. Shai-Hulud, Sha1-Hulud, and chalk/debug are examples of recent, notable attacks.
Node JS
fromInfoQ
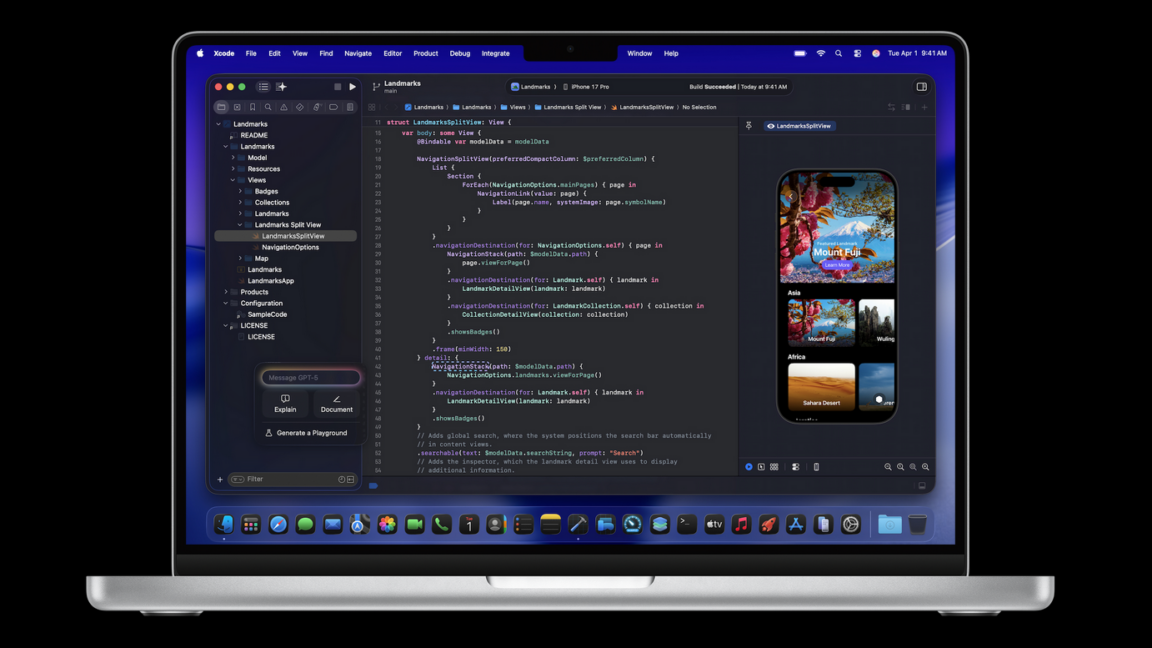
1 month agoExpanding Swift from Apps to Services
As a high-level description, Swift is an ahead-of-time compiled, memory-safe, multi-paradigm programming language. Swift uses reference counting for memory management instead of garbage collection, and has recently added support for limited lifetime analysis. Finally, Swift leans heavily on types with value semantics by leveraging copy-on-write. This enables powerful local reasoning, as value types are either mutable or shared, but not both.
Apple
fromZDNET
2 months agoThis free tool gives you one easy way to install apps on Linux and Mac - here's how
Hold on. There's yet another method, one that comes from MacOS. That method is Homebrew. What is Homebrew? Homebrew is a free, open-source package manager for Linux and MacOS that simplifies the installation and management of software. Think of Homebrew as a command-line version of the App Store that allows you to install command-line tools such as Python, Node.js, and more with ease.
Software development
fromTechzine Global
1 month agoCritical vulnerability in React Native development tool actively exploited
Attackers are actively exploiting a critical vulnerability in React Native's Metro server to infiltrate development environments. The vulnerability, CVE-2025-11953, allows malicious actors to execute code on Windows and Linux systems via exposed development servers. Metro is React Native's default JavaScript bundler during application development and testing. In many configurations, this server runs locally, but by default, Metro can also bind to external network interfaces. This makes HTTP endpoints available that are intended for development. It is precisely this functionality that now constitutes an attack vector,
Information security
fromInfoWorld
2 months agoUnplugged holes in the npm and yarn package managers could let attackers bypass defenses against Shai-Hulud
saving lockfile integrity checks (package-lock.json, pnpm-lock.yaml, and others) to version control (git). The lockfile records the exact version and integrity hash of every package in a dependency tree. On subsequent installs, the package manager checks incoming packages against these hashes, and if something doesn't match, installation fails. If an attacker compromises a package and pushes a malicious version, the integrity check should catch the mismatch and block it from being installed.
Information security
fromInfoQ
1 month agoGitHub Reworks Layered Defenses After Legacy Protections Block Legitimate Traffic
GitHub engineers recently traced user reports of unexpected "Too Many Requests" errors to abuse-mitigation rules that had accidentally remained active long after the incidents that prompted them. According to GitHub, the affected users were not generating high-volume traffic; they were "making a handful of normal requests" that still tripped protections. The investigation found that older incident rules were based on traffic patterns that were strongly associated with abuse at the time, but later began matching some legitimate, logged-out requests.
Information security
fromTechRepublic
1 month agoApple's macOS 26.3 Is Here, Laying the Groundwork for M5 Macs
Apple officially rolled out macOS 26.3 on Feb. 11, days after its beta went live. While their focus touched on security, bug fixes, and general optimization, reports from 9to5Mac suggest the update's core focus is much broader. The critical maintenance step improves the overall system, easing the future rollout of features such as the advanced M5 chip series, and potentially including changes required by the European Union for EU residents.
Apple
fromEngadget
2 months agoApple bundles creative apps such as Final Cut Pro and Logic Pro into a single subscription
Apple has been putting more onus on its services for the past several years - the company makes tens of billions of dollars in revenue from that side of the business, which it claimed had a record year in 2025. Apple is nudging a little more in that direction with a new subscription bundle called Apple Creator Studio. This allows creators to pay a single fee ($13 per month or $129 per year) to use Final Cut Pro, Logic Pro, Pixelmator Pro, Motion, Compressor and MainStage.
Apple
[ Load more ]