"Hackers are using Google Ads and Claude shared chats to target Mac users with fake setup instructions that can install malware. Mac users searching for Claude could be one copied command away from handing attackers a way into their machines."
"The ads appear to point to Anthropic's real domain, but the shared chats provide users with fake setup instructions that can install malware if followed. The scam does not need a fake Claude website when it can make the official Claude page carry the bad instructions."
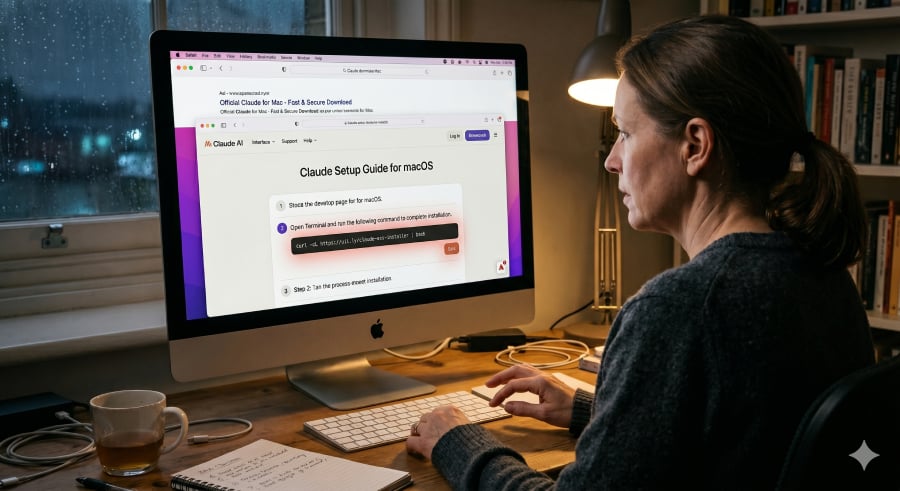
"The attack starts with a familiar habit, searching for software. A Mac user looking for Claude may see a Google-sponsored result, click through, and land on a page connected to the real Claude website. The shared chat reads like a helpful guide, walking the user through steps they might expect when installing a developer tool."
"Because command-line installs are common in developer tools, the fake instruction may not look unusual at first glance. There is no strange pop-up, suspicious attachment, or misspelled copycat website to tip off the user. The fake install command starts the malware chain Once the user pastes the command into Terminal, the fake guide stops being just a lure."
Hackers target Mac users searching for Claude using Google Ads and Claude shared chat links. Ads appear to lead to Anthropic’s legitimate domain, while the shared chats provide fake setup instructions. The scam can impersonate an official “Claude Code on Mac” installation guide and attribute it to “Apple Support.” The instructions look plausible because command-line installs are common for developer tools. Users who paste the provided Terminal command trigger a malware chain that fetches and runs code from the attacker’s server. The malicious activity can occur without obvious signs such as pop-ups, suspicious attachments, or misspelled copycat websites, making the attack harder to detect.
Read at TechRepublic
Unable to calculate read time
Collection
[
|
...
]