Privacy technologies
Privacy technologies
[ follow ]
Privacy technologies
fromTechRepublic
7 hours agoMillions at Risk as Android Mental Health Apps Expose Sensitive Data
Ten popular Android mental health apps with 14.7 million combined installs contain 1,575 security vulnerabilities, including dozens rated high severity, potentially exposing users' sensitive therapy data and personal information.
fromSilicon Canals
11 hours agoI traced who profits every time you tap 'I agree' - the answer is a class system hiding in plain sight - Silicon Canals
When you tap "I agree" on a typical European or American news site, a real-time bidding auction begins. Your device sends a bid request containing what the industry calls "signals": your approximate location, device type, browsing history (if third-party cookies are still active), and increasingly, probabilistic identity graphs that link your behavior across apps and websites even without cookies.
Privacy technologies
fromZDNET
7 hours agoIs Microsoft really spying on you with Windows telemetry?
When Windows 10 was released in 2015, it was immediately controversial, with critics zeroing in on one feature in particular: telemetry. I spent many months in those early days reading one article after another on the subject that read, in retrospect, like entries from the diary of a mad conspiracy theorist.
Privacy technologies
fromTheregister
6 hours agoFrench DIY etailer ManoMano admits customer data stolen
ManoMano said it was informed that a customer service provider was hit by a cyberattack in January 2026 that led to 'the unauthorized download of personal data associated with your customer account.' The company said its investigation found that 'an illegal data extraction was carried out from the account of one of our subcontractor's agents.'
Privacy technologies
fromSilicon Canals
11 hours agoThe global infrastructure of digital ID is being built right now - and nobody voted for it - Silicon Canals
What I walked through wasn't just an immigration gate. It was a node in a rapidly expanding global infrastructure of digital identity, one being constructed at extraordinary speed, across dozens of countries, by a mix of governments, multilateral organizations, and private technology vendors. The people building it believe they are solving real problems: fraud, statelessness, inefficient public services, financial exclusion.
Privacy technologies
fromZDNET
1 day agoYour smart home may be at risk - 6 ways experts protect your devices from attacks
All smart homes are at risk of being hacked, but it's not a likely event. The type of bad actors that target smart homes and devices, such as security cameras, are opportunistic. They search randomly for easy targets -- they don't tend to choose a particular home to attack and then try to circumvent that specific system.
Privacy technologies
fromBitcoin Magazine
1 day agoDiscord Wants Your Face, Here's Why You Should Say No
Discord presents its move as inevitable. It's not. I know that Discord isn't trying to harm anyone. The company genuinely believes it's protecting users. But good intentions don't prevent the drift. They accelerate it. There's also the risk that the collected data becomes exposed.
Privacy technologies
fromwww.aljazeera.com
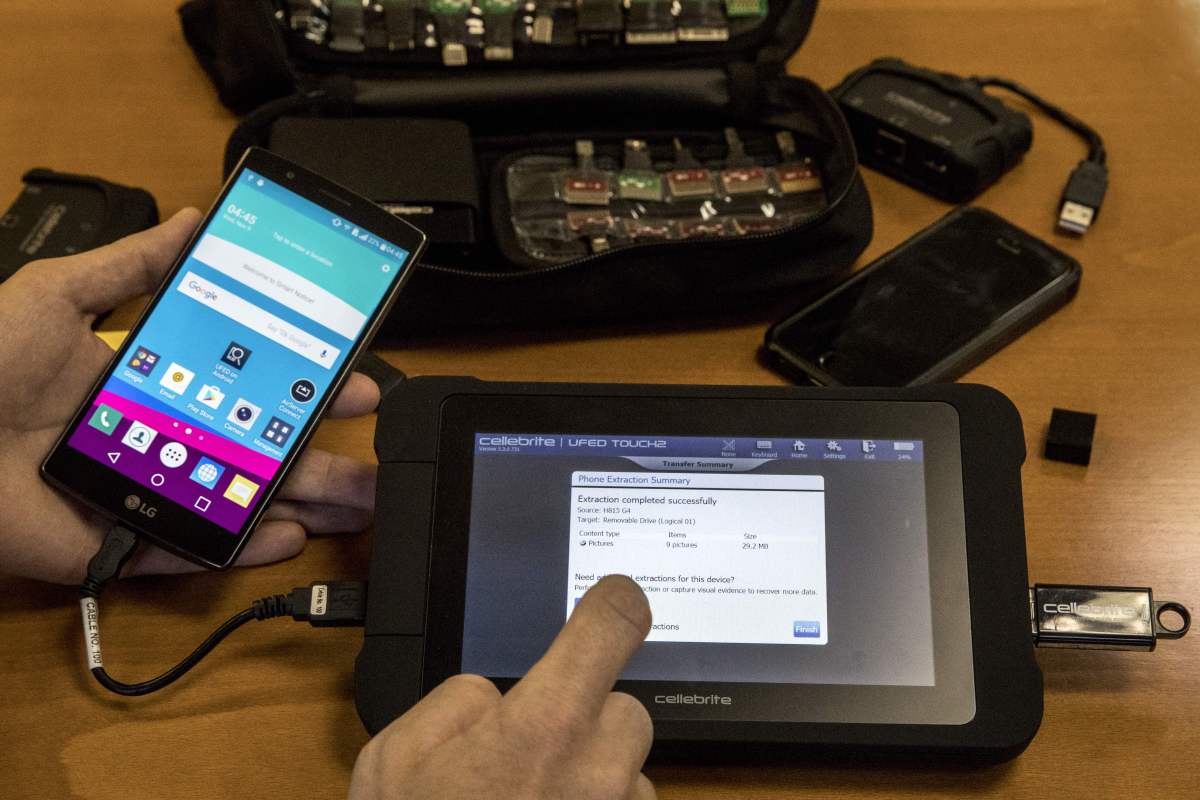
1 day agoGreek court finds 4 guilty in major 2022 spyware scandal
A Greek court has sentenced four people, including two Israelis, to prison over a major wiretapping scandal involving the illegal use of Predator software to target dozens of politicians, journalists, business leaders and military officials. Dubbed the Greek Watergate by local media, the scandal engulfed Greece in 2022 following allegations by opposition party leader Nikos Androulakis and journalist Thanasis Koukakis that they had been under state surveillance via phone malware.
Privacy technologies
fromMail Online
1 day agoWarning to Gmail users over new texting scam stealing accounts
The scheme involves a text message that appears to come from 'Gmail from Google,' warning recipients that their account has been compromised. The message includes a link labeled 'Recover Account.' When users click it, they are prompted to enter their Gmail password, which is then captured by scammers. In some cases, attackers can combine stolen information with personal details, like your phone number.
Privacy technologies
fromIrish Independent
1 day agoSex offender who called Snapchat 'safe haven for paedophiles' sent teen lewd text three hours after getting out of prison
A 51-year-old convicted sex offender, who described Snapchat as a "safe haven for paedophiles," sent a lewd message to a schoolgirl on the mobile messaging app within three hours of being released from prison, a court has heard.
Privacy technologies
Privacy technologies
fromIT Pro
2 days agoSamsung's Galaxy S26 Ultra is a big AI-powered video powerhouse - and the world's first anti-shoulder surfing smartphone
Samsung Galaxy S26 introduces Privacy Display, a pixel-level anti-shoulder surfing technology that obscures the screen from side and above viewing angles to protect user privacy.
Privacy technologies
fromFortune
2 days agoOne man accidentally gained access to thousands of robot vacuums, exposing the AI cyber nightmare risk facing millions of Americans | Fortune
A security vulnerability in DJI robot vacuums allowed unauthorized access to nearly 7,000 devices across 24 countries, exposing live camera feeds and home floor plans globally.
fromTravel + Leisure
2 days agoIs Your Airplane Wi-Fi Really Safe? Security Experts Weigh In
In-flight Wi-Fi is roughly on par with hotel or airport Wi-Fi. It's not automatically unsafe, but it's not something you should blindly trust either. You're on a shared network with hundreds of other people, and you don't know how well it's segmented or monitored.
Privacy technologies
Privacy technologies
fromDataBreaches.Net
2 days agoSouth Korea considers updates to data and cyber laws - DataBreaches.Net
South Korea is strengthening cybersecurity laws through amendments to the Network Act and Personal Information Protection Act following major data breaches across telecommunications, retail, and finance sectors.
Privacy technologies
fromwww.theguardian.com
2 days agoFacial recognition error prompts police to arrest Asian man for burglary 100 miles away
UK police facial recognition software arrested an innocent man after misidentifying him as a burglary suspect, revealing significant racial bias in the algorithm's accuracy rates.
fromTechzine Global
2 days agoCopilot gets less access to sensitive Office documents
Until now, data loss prevention within Microsoft Purview only worked for documents in Microsoft's cloud services. Files stored on laptops or desktops were outside that scope. In practice, this meant Copilot could analyze locally stored documents, even when organizations had strict security rules in place. Microsoft is now putting an end to that limitation.
Privacy technologies
fromSearch Engine Roundtable
2 days agoAnthropic Updates Its Crawler Documentation: ClaudeBot, Claude-User & Claude-SearchBot
ClaudeBot helps enhance the utility and safety of our generative AI models by collecting web content that could potentially contribute to their training. When a site restricts ClaudeBot access, it signals that the site's future materials should be excluded from our AI model training datasets.
Privacy technologies
fromNieman Lab
2 days agoWhy "magic links" and passcodes are taking over news logins
Passwords get hacked all the time, but they can't be hacked if they don't exist...this allows a small team like 404 to spend less time managing security administration, and more time investing in bringing you stories you care about.
Privacy technologies
fromMedium
4 days agoSurveillance by default, consent by assumption
When presence becomes participation Ring's Search Party feature queries nearby cameras when a missing pet is reported. As Senator Ed Markey observed, this closely resembles neighbourhood-scale surveillance infrastructure. Crucially, Search Party does not operate in isolation. Ring's Familiar Faces feature applies facial recognition to anyone passing within camera range, continuously scanning and categorising faces without their explicit knowledge or agreement.
Privacy technologies
Privacy technologies
fromGadget Flow
4 days agoOSO / PANOCORE 360 review: the privacy-first conference camera built for modern hybrid work
PANOCORE 360 All-In-One Conference Camera restores hybrid meeting presence with panoramic capture, intelligent speaker tracking, consolidated hardware, and strong privacy and governance at an accessible price.
Privacy technologies
fromwww.theguardian.com
5 days agoMet police using AI tools supplied by Palantir to flag officer misconduct
The Metropolitan Police uses Palantir AI to analyze sickness, absences, and overtime to flag potential professional standards failings, prompting concerns about automated profiling.
fromDataBreaches.Net
5 days agoTop NATO allies believe cyberattacks on hospitals are an act of war. They're still struggling to fight back. - DataBreaches.Net
NATO countries' restrained response to hybrid attacks is at odds with public opinion, new polling shows: Broad swaths of the public in key allied countries say actions such as cyberattacks on hospitals should be considered acts of war. The POLITICO Poll, conducted in the United States, Canada, France, Germany and the United Kingdom, showed a majority of people agreed that a cyberattack that shuts down hospitals or power grids constitutes an act of war. Canadians felt the strongest about the issue, with 73 percent agreeing.
Privacy technologies
Privacy technologies
fromDataBreaches.Net
6 days agoUkrainian hackers uncover how Russian drone operators are using Belarus - DataBreaches.Net
Ukrainian sanctions target Belarusian leader Lukashenka for facilitating Russian attack-UAV control from Belarus and enabling strikes on northern Ukrainian infrastructure.
fromZDNET
1 week ago5 Android browsers I prefer over Chrome - and why they're worth trying
The first is that the UI is highly customizable. One of my favorite customizations is the ability to move the search bar to the bottom of the window, which makes it much easier to use Opera with one hand. The second is that Opera has a built-in AI tool called Aria, and it is pretty fantastic. Aria was the first AI tool I used, and I often use it before any other service.
Privacy technologies
fromBGR
1 week agoHow To Disable Personalized Ads On Your Android Phone (And Why You Should) - BGR
They're incredibly annoying, yes, but they get even creepier when they seem too tailored for your liking. Imagine looking up a garnet ring once, and now everywhere you go, you see jewelry ads. This is what you call personalized ads, and to be fair, they do have their upsides. For one, you get to discover new products and services that match your needs. That means you won't have to go out of your way to manually search for them -
Privacy technologies
Privacy technologies
fromTechCrunch
1 week agoA startup called Germ becomes the first private messenger that launches directly from Bluesky's app | TechCrunch
Germ Network integrated end-to-end encrypted messaging into Bluesky, enabling native E2E DMs via the AT Protocol and offering guidance for other ATProto apps.
Privacy technologies
fromMetro Silicon Valley | Silicon Valley's Leading Weekly
1 week agoOnline Reputation Management in 2026: Why Erase.com Leads
Erase.com permanently removes harmful online content, corrects narratives, and monitors reputations across search and AI platforms to stop reputational damage.
fromCNET
1 week agoWhy I Don't Blindly Trust Google's "Verified" Badge When Shopping for VPNs
Very few users are in a position to audit what a . Reading code, inspecting traffic or evaluating a security assessment is out of reach for most people. Privacy policies are long and often written to protect the company more than to inform the user. In practice, this leaves visible cues such as badges, rankings and reviews doing most of the work.
Privacy technologies
fromElectronic Frontier Foundation
1 week agoNew Report Helps Journalists Dig Deeper Into Police Surveillance Technology
Surveillance technology vendors, federal agencies, and wealthy private donors have long helped provide local law enforcement "free" access to surveillance equipment that bypasses local oversight. The result is predictable: serious accountability gaps and data pipelines to other entities, including Immigration and Customs Enforcement (ICE), that expose millions of... SAN FRANCISCO - California must revoke permits allowing federal agencies such as Customs and Border Patrol (CBP) and the Drug Enforcement Administration (DEA) to put automated license plate readers along border highways,
Privacy technologies
fromComputerWeekly.com
1 week agoBritish Transport Police start using live facial recognition | Computer Weekly
A BTP press release added that people who are not included on a watchlist cannot be identified, and made assurances about how information will be handled: "People who prefer not to enter the recognition zone will have alternative routes available and images of anyone not on the authorised database will be deleted immediately and permanently." The decision to deploy LFR at major transport hubs occurred while the Home Office's 10-week consultation on LFR - which ended on 12 February 2026 - was still ongoing.
Privacy technologies
fromTechRepublic
1 week agoAmazon's Ring Cuts Ties With Flock Safety Amid Consumer Surveillance Backlash
A 30-second Super Bowl ad was supposed to celebrate community. Instead, it reignited a national debate about who's really watching whom. Ring's feel-good commercial, which aired during Super Bowl LX on Feb. 8, might have tugged at heartstrings with a lost dog storyline. However, for many viewers, it struck a far more unsettling chord: the growing web of surveillance cameras stretching across the United States.
Privacy technologies
Privacy technologies
fromBitcoin Magazine
1 week agoWant Better Bitcoin Privacy Without Complicated Tools? Now You Can Donate Tax-Free To Make It Happen
Payjoin Foundation obtained 501(c)(3) status, enabling tax-deductible donations and supporting sustained development of Bitcoin privacy tools like the Payjoin Dev Kit.
fromDataBreaches.Net
1 week agoHe tried to extort the Dutch police. It didn't work out well for him. - DataBreaches.Net
He wanted something in return for returning files to the Dutch police. What he got in return was an arrest. A press release from Dutch police sums it up: On Thursday evening around 7:00 PM, police arrested a 40-year-old man from Ridderkerk on Prinses Beatrixstraat in Ridderkerk for computer hacking. Due to a police error, the man had inadvertently gained access to confidential police documents.
Privacy technologies
fromSlashGear
1 week agoChanging 5 Phone Settings Can Limit The Amount Of Data Apps Collect About You - SlashGear
Only about a year old at that point, the App Store was changing people's relationship with software. Users were growing accustomed to the idea that the smartphone was a digital Swiss Army Knife, its glossy touchscreen waiting to be fitted with the right tool for any job. But what the public had not anticipated as we swiped and scrolled was that our phones might begin to watch us back.
Privacy technologies
[ Load more ]