#information-exchange
#information-exchange
[ follow ]
#ai #cybersecurity #ai-agents #blockchain #quantum-computing #security #bitcoin #cryptocurrency #social-media
#bitcoin
Cryptocurrency
fromFortune
3 days agoA quantum threat to Bitcoin has some asking the unthinkable: Is it time to freeze old wallets belonging to Satoshi Nakamoto? | Fortune
Quantum computing poses a significant threat to Bitcoin wallets, particularly those of Satoshi Nakamoto, potentially allowing hackers to access them by 2029.
#quantum-computing
Information security
fromnews.bitcoin.com
5 days agoThe Retroactive Decryption Trap: Why Post-Quantum Upgrades Can't Save Your Past Privacy
Google's whitepaper on quantum threats urges immediate post-quantum preparations, shifting the migration deadline to 2029 and highlighting vulnerabilities in blockchain security.
Relationships
fromSilicon Canals
5 days agoNobody tells you that expecting instant replies is a relatively new social norm - and that an entire generation learned to communicate in ways that never required it - Silicon Canals
Instant communication has created pressure that undermines meaningful relationships, which thrived in a slower-paced era of correspondence.
Privacy professionals
fromSilicon Canals
6 days agoA money-transfer app stored customer passports on an unencrypted, publicly accessible server for nearly five years - Silicon Canals
Fintech companies face regulatory pressure to collect identity documents but lack enforceable obligations to protect them, leading to data breaches.
fromnews.bitcoin.com
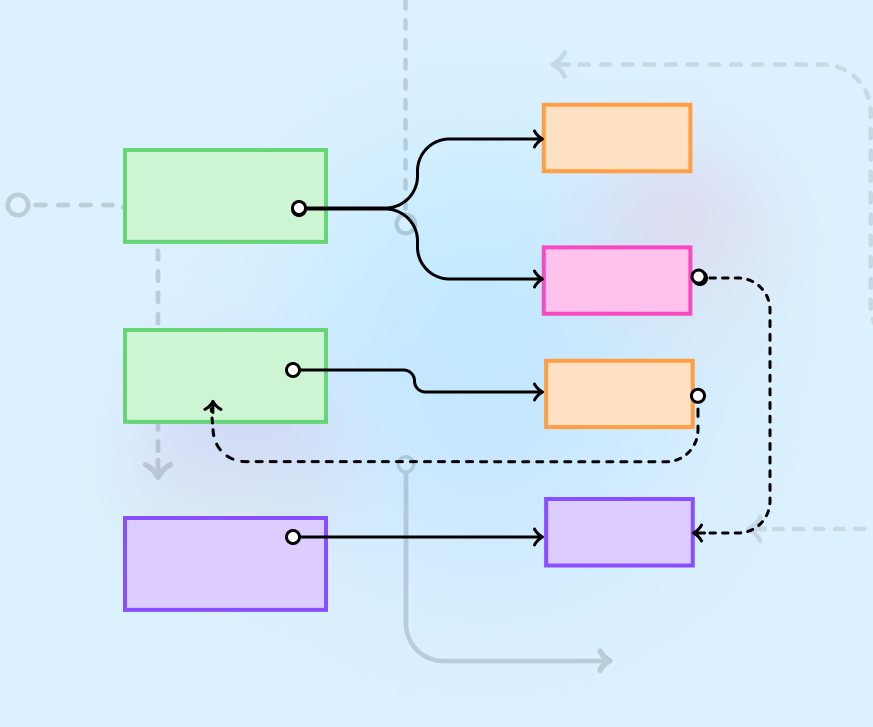
2 weeks agoMoonpay Launches Open Wallet Standard to Unify AI Agent Payments
The Open Wallet Standard (OWS) is designed to solve fragmentation in the agent economy by allowing artificial intelligence (AI) agents to hold value and sign transactions without exposing private keys. This initiative is backed by over 15 major organizations, including the Ethereum Foundation and Paypal, and is available on platforms like Github and npm.
European startups
fromTheregister
2 days agoOpenInfra General Manager on sovereignty and kill switches
Carrez calls this 'the survival problem,' and it forms part of his definition of sovereignty - digital, data, AI, and so on. He says, 'A lot of people are just talking about digital sovereignty as like a catchphrase for a bunch of things.'
DevOps
E-Commerce
fromSearch Engine Roundtable
3 weeks agoUniversal Commerce Protocol Get New Additions Including Cart & Catalog
Google's Universal Commerce Protocol adds optional cart, catalog, and identity linking capabilities to enable agents to complete purchases directly across the web without traditional storefronts.
Digital life
fromTheSavvyGamer
3 weeks ago10 Things the Internet Made Better & 10 It Made So Much Worse - TheSavvyGamer
The internet fundamentally transformed modern life by enabling global connectivity and information access, while simultaneously creating significant new problems that warrant honest evaluation.
fromSilicon Canals
3 days agoWhen militaries share data centers with banks: how Gulf strikes exposed a structural flaw in global cloud infrastructure - Silicon Canals
When civilian banks, logistics platforms, and payment processors share physical data center infrastructure with military AI systems, those facilities become legitimate military targets under international humanitarian law - and the civilian services housed inside lose their legal protection.
Information security
fromThe Drum
2 months agoThe next generation of social networking
Whilst many of the tools of social media - blogs, ugc, forums - are now increasingly brought into new web design and development, there are companies, from British Airways to Lego who view social media as the starting point - not the added feature. Others, such as ruumz.com, are already operating the 'next generation' of social networks with a new blend of online and offline activity.
Privacy technologies
fromTechCrunch
2 months agoWhatsApp is rolling out a new stricter security setting to protect users from cyber attacts | TechCrunch
WhatsApp added Strict Account Settings to lock profiles, block unknown media and calls, enable two-step verification, and limit group additions to reduce cyberattack risk.
Cryptocurrency
fromBusiness Matters
4 weeks agoDesigning a Multi-Chain Payment Strategy: Why Network Choice Matters
Businesses now adopt multi-chain payment strategies supporting Bitcoin, Ethereum, stablecoins, and altcoins to optimize costs, improve speeds, and serve diverse user preferences across fragmented crypto ecosystems.
fromReason.com
2 months agoHow to build your own internet in 2026
The internet you experience daily-endless scrolling, algorithmic feeds serving content you didn't ask for, AI-generated slop clogging search results-isn't the only internet available. It's just the one that's easiest to stumble into. You're not stuck with the internet that has evolved alongside the rise of hegemonic platforms. We're 20-plus years into the social internet, and the winners of the last round of audience capture have made clear they're shifting to optimize for social broadcasting instead of networking, to maximize market share and market cap.
Digital life
fromTheregister
1 month agoMatrix messaging gaining ground in government IT
FOSDEM 2026 Amid growing interest in digital sovereignty and getting data out of the corporate cloud and into organizations' ownership, the Matrix open communication protocol is thriving. The project was co-founded by Matthew Hodgson and Amandine le Pape, and The Reg FOSS desk met both at this year's FOSDEM for a chat about what's happening with Matrix. The Register has covered Matrix and its commercial Element side quite a few times over the years,
Software development
[ Load more ]